Note
For the previous version of User Profiles, see User profiles.
For the previous version of User Profiles, see User profiles.
- View user information
- Add users
- Resend an invitation
- Edit a user’s information
- Enable and disable users
- Manage multi-factor authentication
- Enable single sign-on authentication
Viewing user information
To view user information, go to Control center > User profiles.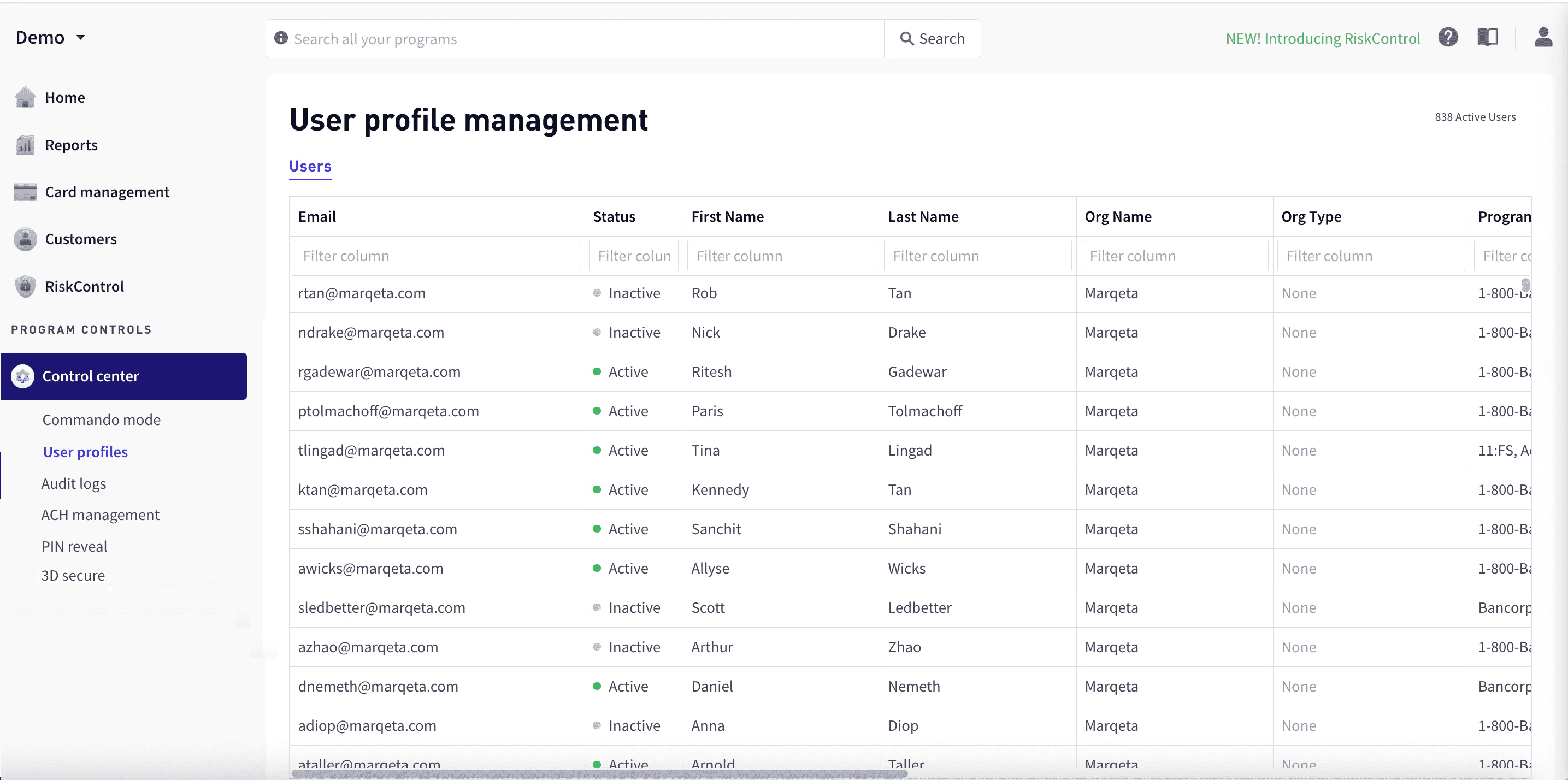
| Column | Description |
|---|---|
| The user’s email address. An invitation to join is sent to this address. | |
| Status | The user’s status: Active or Disabled. |
| First Name | The user’s first name. |
| Last Name | The user’s last name. |
| Org Name | The user’s organization. |
| Org Type | The type of organization, such as Customer, Bank, or Card Network. |
| Programs | Programs whose information the user can view. |
| Date Created | The date that the user was added. |
| Date Updated | The most recent date that the user’s information was updated. |
Filtering by column
To filter rows by column, enter the sequence of letters you want to filter on in the text box at the top of the column. As you type, the matching rows are filtered dynamically.Adding users
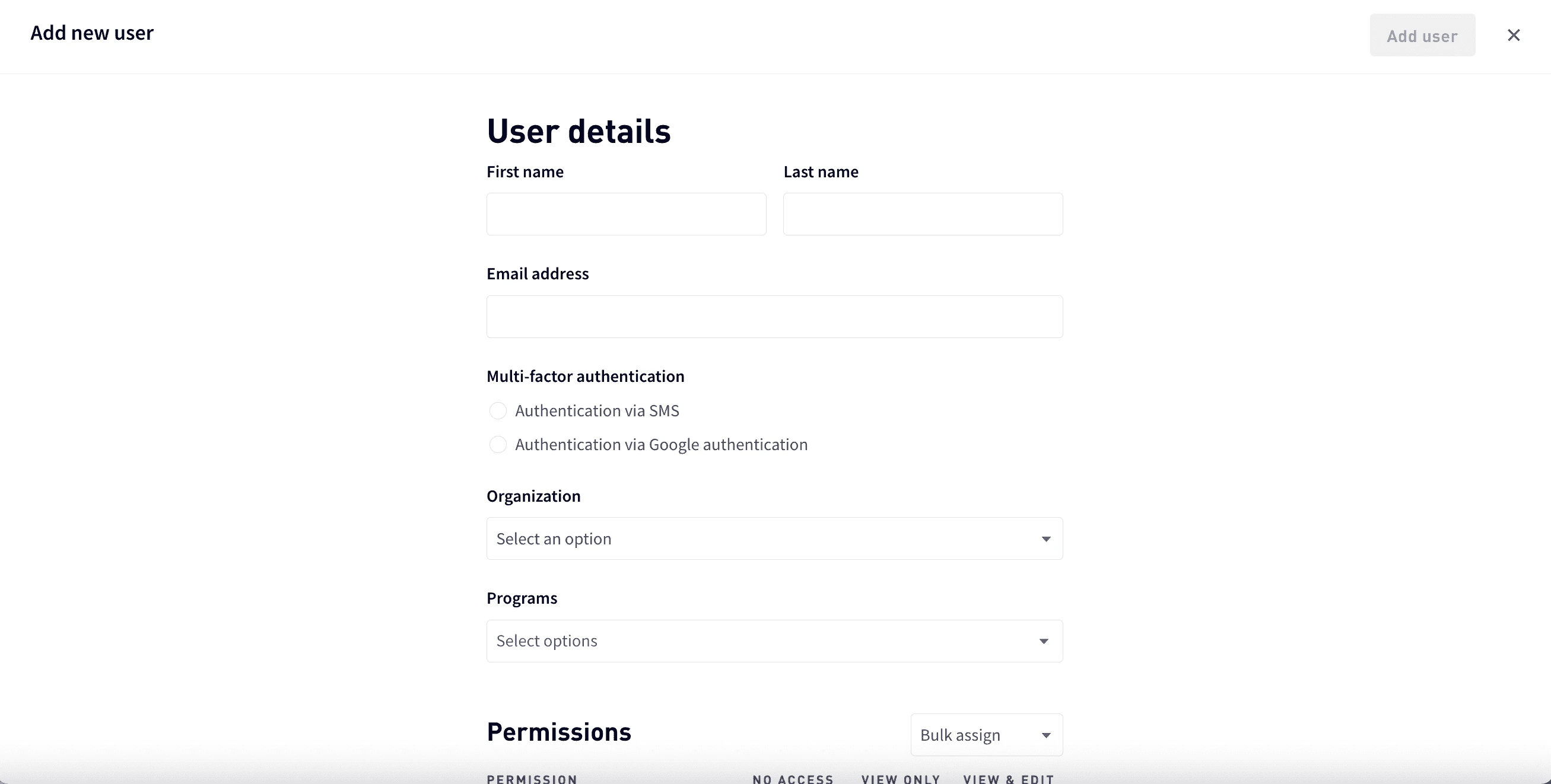
To add a user:For Multi-factor authentication, choose Authentication via SMS or Authentication via Google authentication. For more information, see Managing multi-factor authentication.
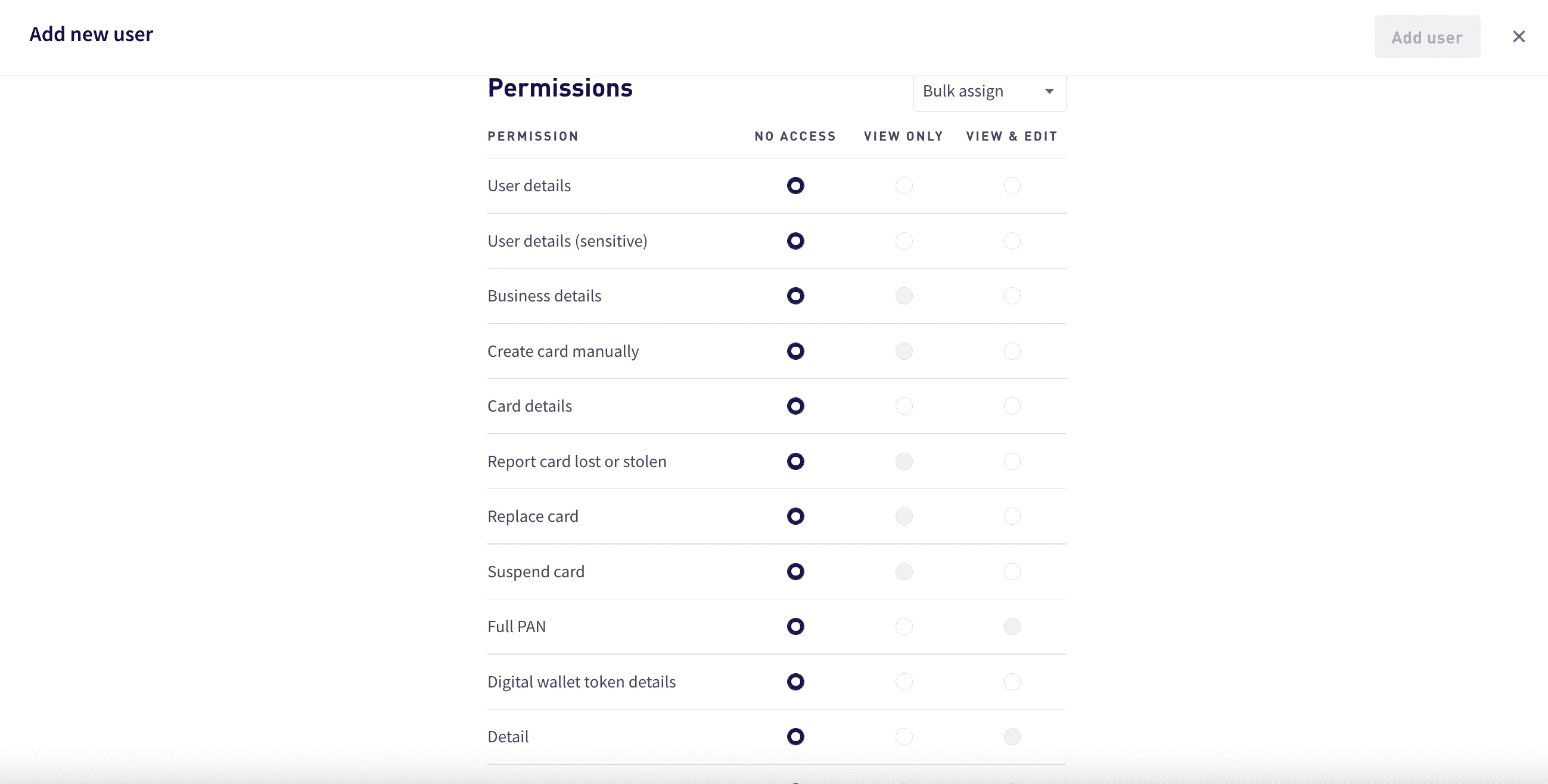
To assign permissions, either assign an access level for each permission or use bulk assign:
- For each permission, select an access level. Access levels that are not available for a permission are grayed.
-
For bulk assign, select Bulk assign and then select the access level for all permissions— No access, View only, or View and edit.
Note
By default, access to personally identifiable information (PII) is denied. Users should be granted the lowest level of access required to fulfill their job responsibilities. Access can only be granted with accordance to your company and the issuing bank’s privacy and information security policies. If a user needs access to PII, contact your Marqeta representative.
By default, access to personally identifiable information (PII) is denied. Users should be granted the lowest level of access required to fulfill their job responsibilities. Access can only be granted with accordance to your company and the issuing bank’s privacy and information security policies. If a user needs access to PII, contact your Marqeta representative.
Permissions
The following table shows the Marqeta Dashboard permissions and available access levels for each. For details on the specific access that each permission provides, see Access level details.| Permission | Available Access Levels | Available Access Levels | Available Access Levels |
|---|---|---|---|
| Card management | |||
| Card products | No access | View only | - |
| Create card manually | No access | - | View and edit |
| Card details | No access | View only | View and edit |
| Report card lost or stolen | No access | - | View and edit |
| Replace card | No access | - | View and edit |
| Suspend card | No access | - | View and edit |
| Control center | |||
| Invoke Commando Mode | No access | View only | View and edit |
| 3DS settings | No access | View only | View and edit |
| Audit logs | No access | View only | - |
| Customers | |||
| Marqeta Dashboard - Access Management | No access | View only | View and edit |
| User details | No access | View only | View and edit |
| User details (sensitive) | No access | View only | View and edit |
| Account holder details | No access | View only | View and edit |
| Account holder details (sensitive) | No access | View only | View and edit |
| Full account number | No access | View only | - |
| Manage ACHO transfers | No access | - | View and edit |
| Cancel ACHO program funding | No access | - | View and edit |
| Business details | No access | View only | View and edit |
| Full primary account number (PAN) and card verification value (CVV) | No access | View only | - |
| Set personal identification number (PIN) (sensitive) | No access | - | View and edit |
| ACH program funding | No access | View only | View and edit |
| Digital wallets | |||
| Digital wallet token details | No access | View only | View and edit |
| Program controls | |||
| Program configuration | No access | - | View and edit |
| Granular permissions | No access | View only | - |
| Inventory management | No access | - | View and edit |
| Reports | |||
| Analytics | No access | View only | - |
| Compliance | No access | View only | - |
| Detail | No access | View only | - |
| Cross border fees | No access | View only | - |
| Currency conversion fees | No access | View only | - |
| Interchange | No access | View only | - |
| Stories | No access | View only | - |
| Personal identifiable information | No access | View only | - |
| 3DS reporting | No access | View only | - |
| Commercial credit | No access | View only | - |
| Loads settlement date | No access | View only | - |
| PIN interchange | No access | View only | - |
| Risk Control | |||
| Transaction review manager | No access | - | View and edit |
| Disputes | No access | - | View and edit |
| Process disputes (EU only) | No access | - | View and edit |
| Other | |||
| Return direct deposit | No access | - | View and edit |
Access level details
The following table shows the specific access in the dashboard granted for each permission and access level:| Permission | Access Level Details |
|---|---|
| Card management | |
| Card products | View only – Users with this permission can: - View all card products available in the program. - View the card product details and spend controls for each card product in the program. |
| Card details | View only – Users with this permission can: - View all information in the Card Details section except full PAN. - View card transaction, history, card transitions, and digital wallet tokens summary. View and edit – Activate and terminate a card. |
| Report card lost or stolen | View and edit – Complete the report card workflow for a lost or stolen card in the Card Details section. |
| Replace card | View and edit – Complete the replace card workflow in the Card Details section. |
| Suspend card | View and edit – Complete the lock card workflow in the Card Details section. |
| Control center | |
| Invoke Commando Mode | View only – View all Commando Mode configurations. View and edit – Enable or disable all available Commando Mode configurations for the program. |
| 3DS settings | View only – View 3DS settings and configurations for the program. View and edit – View the 3DS settings and edit the configurations for the program. |
| Audit logs | View only – View Marqeta Dashboard user action history for the program. |
| Customers | |
| Marqeta Dashboard - Access Management | View only – Provides view access to the User Profile Management dashboard. Users with this permission can see a list of Marqeta Dashboard users. View and edit – In addition to viewing the User Profile Management dashboard, users with this permission can edit user profiles and permissions. Possible access includes the ability to: - Create user profiles with required permissions. - Edit user profiles. - Edit and reset multi-factor authentication. - Assign permissions and programs to other dashboard users. |
| User details | View only – Users with this permission can: - View all information in the User Details section except identification information. - View the cardholder’s associated cards, digital wallet tokens, and transactions summary but not all the card details, token details, and transaction details. View and edit – Users with this permission can: - View and edit all information in the User Details section except identification information. - Change status of the user and add notes. |
| User details (sensitive) | View only – View all identification information in the User Details section. View and edit – View and edit all identification information in the User Details section. |
| Account holder details | View only – Users with this permission can: - View all information in the Account Holder Details section except personally identifiable information. - View the account holder’s associated cards, digital wallet tokens, and transactions summary but not all the card details, token details, and transaction details. View and edit – Users with this permission can: - View and edit all information in the User Details section except personally identifiable information. - Change status of the user and add notes. |
| Account holder details (sensitive) | View only – View all information in the Account Holder Details - Identification section, including personally identifiable information. View and edit – View and edit all information in the Account Holder Details - Identification section, including personally identifiable information. |
| Full account number | View only – View all information in the Account Holder Details - Identification section, including personally identifiable information. |
| Manage ACHO transfers | View and edit – View and edit all information in the Account Holder Details - Identification section, including personally identifiable information. |
| Cancel ACHO program funding | View and edit – View previous ACH transfers and create new ACHO program funding transfers. |
| Business details | View only – Users with this permission can: - View all information in the Business Details section except sensitive information. - View the business’ associated child users, digital wallet tokens, and transactions summary but not all the user details and token details. View and edit – Users with this permission can: - View and edit most information in the Business Details section except for customers using KYB with Marqeta. - Change status of the user and add notes. - Add notes to the business. |
| Full PAN and CVV | View only – View full PAN in the card art and the Card Details section. |
| Set PIN (sensitive) | View and edit – Set PIN for all card in assigned programs. |
| ACH program funding | View only – View the ACH Program Funding page and the ACH Transfers table for the program. View and edit – View previous ACH transfers and create new ACHO program funding transfers. |
| Digital wallets | |
| Digital wallet token details | View only – View all information in the Digital Wallet Tokens section except full PAN. View and edit – Activate, suspend, and terminate digital wallet tokens. |
| Program controls | |
| Program configuration | View and edit – Users with this permission can: - View and edit programs, card products, accepted countries, MCC groups, and application tokens. - Edit and submit configurations to the Approval queue. |
| Reports | |
| Detail | View only – View detailed transaction-level data in the Reports section. |
| Cross border fees | View only – View cross border fees in the Reports section. |
| Currency conversion fees | View only – View currency conversion fees in the Reports section. |
| Interchange | View only – View the sig_interchange and chargebacks_interchange columns in the Clearing Detail report. |
| Stories | View only – Create charts and visuals. |
| Personally identifiable information (PII) | View only – View cardholders’ personally identifiable information (PII). |
| 3DS reporting | View only – View the 3DS ACS report. |
| Commercial credit | View only – View credit balances by day and hour. |
| Risk Control | |
| Transaction review manager | View and edit – Review transactions and initiate transaction alerts. |
| Disputes | View and edit – Initiate disputes. |
| Process disputes (EU only) | View and edit – Manage and process disputes. |
| Other | |
| Return direct deposit | View and edit – Reverse direct deposits. |
Resending an invitation
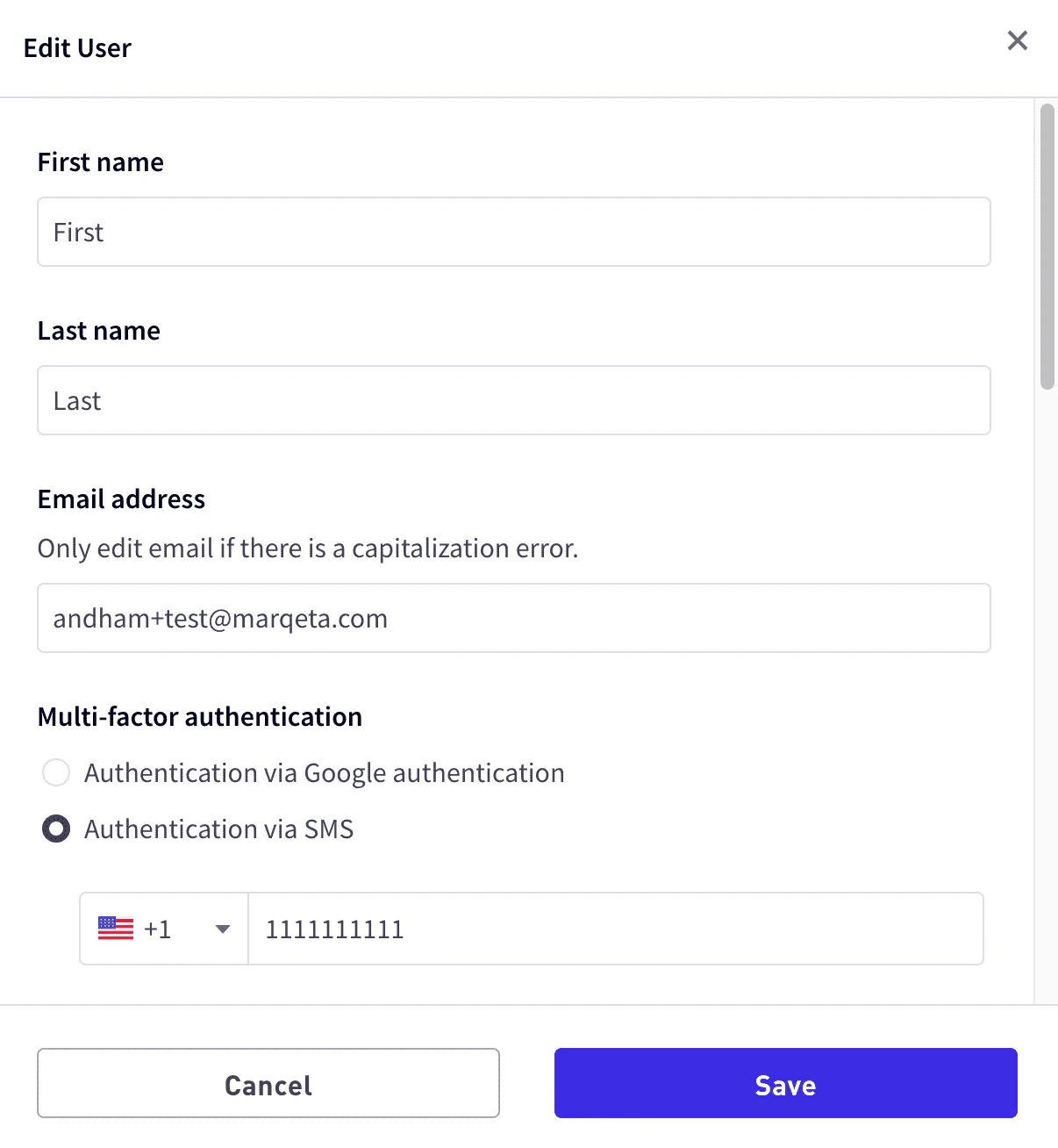
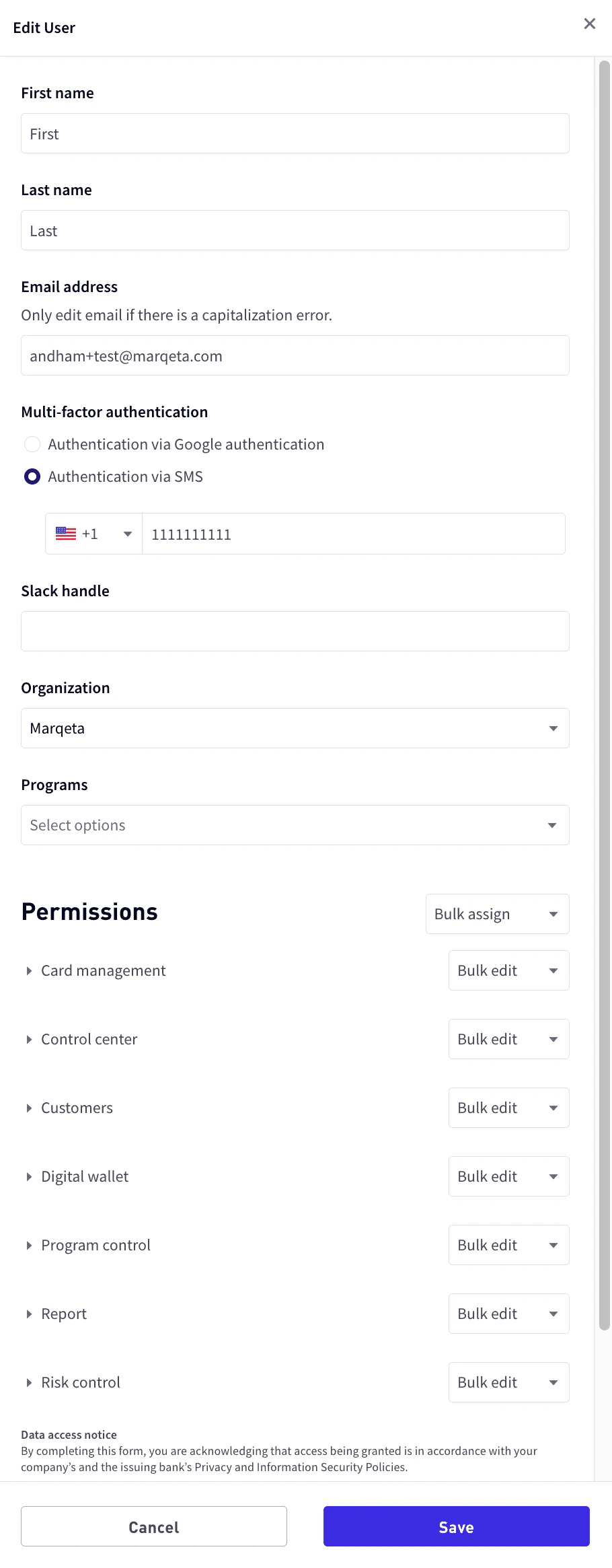
To resend an invitation:Editing user information
To edit a user’s information:At the bottom of the User profile pane, select Edit user.
-
Update any of the user’s basic information, or add and remove programs, permissions, or access levels as necessary. For more information, see Permissions.
Enabling and disabling users
To enable or disable a user:Managing multi-factor authentication
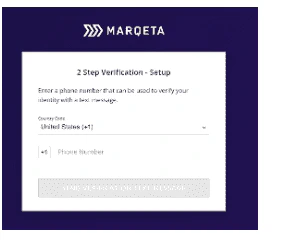
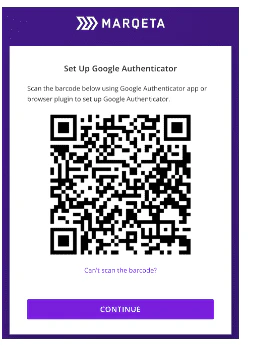
Multi-factor authentication (MFA) is an authentication method that requires the user to provide two or more verification factors to gain access. Marqeta Dashboard requires users to have MFA enabled via SMS or Google’s Time-based One Time Password (TOTP) authenticator. To reset or manage a user’s MFA options, you must have the View and Edit access level for the User Profiles privilege.Resetting multi-factor authentication
You should reset the user’s MFA when a user:- Changes their phone number and needs to authenticate using a new phone number using SMS.
- Changes their mobile device and needs to authenticate using a new device with Google authenticator.
- Deletes their Google authenticator code and needs to rescan the QR code using the same device.
In the Multi-factor authentication section, select either Authentication via Google authentication or Authentication via SMS.
Switching a user’s MFA option
A user’s MFA option can be switched between SMS and Google Authenticator. Switch a user’s MFA option when the user:- Is not receiving SMS messages and would like to switch to Google Authenticator.
- Is an international user who doesn’t use a US phone number and has trouble receiving SMS.
- Would like to switch from SMS to Google Authenticator or switch from Google Authenticator to SMS.
In the Multi-factor authentication section, select either Authentication via Google authentication or Authentication via SMS.
Accessing the Dashboard using MFA
Note
This section describes how users can access the Marqeta Dashboard using multi-factor authentication.
This section describes how users can access the Marqeta Dashboard using multi-factor authentication.
Resetting your MFA access
In some cases, your MFA access may need to be reset—for example, if your device has been lost or stolen. In that case, contact your system administrator to reset your MFA access.Resetting MFA for SMS
If you have SMS MFA enabled and have requested a reset:Resetting MFA for Google Authenticator
If you have Google Authenticator MFA enabled and have requested a reset:Switching your multi-factor authentication option
If you want to switch your MFA option, send a request to your system administrator. You will be prompted to register using either the SMS or Google Authenticator procedure described above.Enabling single sign-on authentication
Single sign-on (SSO) is an authentication method that allows users to log in to multiple applications with one set of credentials. SSO reduces security overhead for system administrators by allowing users to delegate authentication to their external Security Assertion Markup Language 2.0 (SAML 2.0) Identity Provider (IdP) and eliminating the need for users to maintain a separate password to log in to Marqeta Dashboard. When you enable SSO, SSO becomes the exclusive method for your users to log in to Marqeta Dashboard. SSO implementation is based on email domain, so after your email domain is onboarded to SSO, your new and existing users will be automatically provisioned for SSO. You will follow the existing process to add a user in Marqeta Dashboard. Your users will then access Marqeta Dashboard using SSO. If you are a system administrator and prefer your users use SSO, contact your Marqeta representative. Note that email aliases are not valid for SSO with Marqeta Dashboard. Users who use email aliases to access Marqeta Dashboard will lose access after SSO is enabled, so consult with your Marqeta representative if your organization includes such users.Setting up single sign-on authentication
To set up SAML 2.0 authentication in Marqeta Dashboard:Share the service provider with your Marqeta representative.Marqeta will provide you with two URLs, one for SSO and another for audience restriction.
Accessing the Dashboard using SSO
This section describes how users can access the Marqeta Dashboard using single sign-on (SSO) authentication.Note
The Marqeta Dashboard does not currently support IdP-initiated login flows. Marqeta Dashboard users who log in with SSO methods cannot use the application link on their IdP dashboard to log in.
The Marqeta Dashboard does not currently support IdP-initiated login flows. Marqeta Dashboard users who log in with SSO methods cannot use the application link on their IdP dashboard to log in.